The digital landscape increasingly demands secure document workflows‚ and Linux provides robust tools for digitally signing PDFs. Appointment booking software’s growth fuels this need‚ alongside broader digital adoption‚ requiring secure confirmation methods.
Why Sign PDFs on Linux?
Linux offers a compelling platform for PDF signing due to its inherent security features and flexibility. Unlike relying on proprietary software‚ Linux empowers users with open-source tools and granular control over their digital signatures. The rising popularity of appointment scheduling apps‚ and the need to confirm bookings digitally‚ highlights this demand.
Businesses and individuals alike benefit from the ability to digitally sign PDFs on Linux‚ ensuring document authenticity and integrity. This is crucial for contracts‚ legal documents‚ and any sensitive information requiring verification. The increasing adoption of digital technologies‚ as seen in appointment booking software development‚ necessitates secure digital signatures. Furthermore‚ Linux’s command-line capabilities allow for automation and scripting‚ streamlining the signing process for high-volume tasks. It’s a cost-effective and secure solution.
Security Considerations for PDF Signing
When digitally signing PDFs on Linux‚ prioritizing security is paramount. The integrity of your digital signature hinges on protecting your private key. Compromised keys can lead to document forgery and legal repercussions. Robust certificate management‚ utilizing tools like KeyStore Explorer‚ is essential for secure storage and access control.
Furthermore‚ verifying the validity of certificates used for signing is crucial. Ensure the certificate authority (CA) is trusted and the certificate hasn’t been revoked. The growth of appointment booking software and the associated digital confirmations amplify the risk of malicious actors attempting to tamper with documents. Regularly update your signing tools and operating system to patch security vulnerabilities. Employ strong passwords and consider hardware security modules (HSMs) for enhanced key protection‚ especially in business environments.

Methods for Digitally Signing PDFs on Linux
Linux offers diverse methods for PDF signing‚ ranging from user-friendly GUI applications like LibreOffice SignWriter to powerful command-line tools such as `qpdf` and `pdfsig`.
Using LibreOffice SignWriter
LibreOffice SignWriter presents a straightforward graphical interface for digitally signing PDFs on Linux systems. This tool‚ integrated within the LibreOffice suite‚ simplifies the process‚ making it accessible even for users unfamiliar with command-line operations or complex cryptographic procedures.
To utilize SignWriter‚ you’ll first need a digital certificate‚ often stored on a USB token or within your system’s keystore. The application guides you through selecting the appropriate certificate and visually positioning the signature on the document.
SignWriter supports various signature types‚ including visible signatures that appear as an image and invisible signatures embedded within the PDF’s structure. It ensures the integrity and authenticity of your documents‚ confirming the signer’s identity and preventing unauthorized modifications post-signing. The tool’s ease of use makes it a popular choice for routine PDF signing tasks.

Utilizing the `qpdf` Command-Line Tool
The `qpdf` command-line tool offers a powerful and flexible method for digitally signing PDFs on Linux‚ appealing to users comfortable with terminal-based operations. While requiring a steeper learning curve than GUI options‚ `qpdf` provides granular control over the signing process and is ideal for scripting and automation.
Signing with `qpdf` involves specifying the input PDF‚ the digital certificate (typically a PKCS#12 file)‚ the signature password‚ and the output file name. The command utilizes cryptographic algorithms to embed the signature‚ ensuring document integrity and non-repudiation.
Advanced users can leverage `qpdf` for signature verification‚ checking the validity of existing signatures and confirming that the document hasn’t been tampered with. Its efficiency and scripting capabilities make it a valuable asset for managing large volumes of PDF documents and automating signing workflows.
Employing `pdfsig` for PDF Signing
`pdfsig` is a dedicated command-line tool specifically designed for digitally signing PDF documents on Linux systems. It simplifies the signing process compared to more general-purpose tools like `qpdf`‚ offering a streamlined interface focused solely on PDF signatures; This focus makes it a good choice for users who need a straightforward signing solution without extensive configuration.
The tool typically requires a digital certificate in a supported format (like PKCS#12) and the associated password. `pdfsig` then uses this certificate to embed a digital signature within the PDF‚ verifying the document’s authenticity and integrity. It supports various signature algorithms and allows for customization of signature appearance.
Like `qpdf`‚ `pdfsig` can also be used to verify existing signatures‚ ensuring that a PDF hasn’t been altered since it was signed. Its simplicity and dedicated functionality make it a practical option for routine PDF signing tasks.
Graphical User Interface (GUI) Options
For users preferring visual tools‚ several GUI applications on Linux facilitate PDF signing‚ offering user-friendly interfaces and streamlined workflows for document authentication.
Okular PDF Viewer with Digital Signature Support
Okular‚ a versatile and widely-used PDF viewer for Linux‚ incorporates robust digital signature capabilities. It allows users to both sign and verify PDF documents directly within the application‚ eliminating the need for separate signing tools. To sign a PDF in Okular‚ you’ll need a digital certificate installed on your system.
The process is relatively straightforward: open the PDF‚ navigate to the signing option (typically found under the ‘Edit’ or ‘Tools’ menu)‚ select your certificate‚ and draw your signature on the document. Okular supports various signature types and allows you to customize the appearance of your signature. Furthermore‚ it provides tools to validate existing signatures‚ ensuring the document’s authenticity and integrity. This makes Okular a convenient and powerful option for everyday PDF signing needs on a Linux system.
Master PDF Editor for Linux
Master PDF Editor is a powerful and comprehensive PDF editing tool available for Linux‚ offering extensive features including robust digital signature support. Unlike some viewers‚ it’s designed for modification‚ making signing a seamless part of the editing workflow; The application allows you to add digital signatures‚ handwritten signatures (if you have a compatible input device)‚ and even image-based signatures to your PDFs.
To sign‚ open your PDF‚ select the signing tool‚ choose your certificate‚ and place the signature. Master PDF Editor provides options for customizing signature appearance and security settings. It also allows for verifying signatures to ensure document authenticity. Its user-friendly interface and broad feature set make it a strong contender for users needing more than just basic signing functionality‚ especially within a broader PDF editing context.
PDFsam Basic & Enhanced
PDFsam (PDF Split and Merge) offers both a free Basic version and a paid Enhanced version‚ both capable of digitally signing PDFs on Linux. While primarily known for its PDF manipulation capabilities – splitting‚ merging‚ rotating‚ and extracting pages – the Enhanced version includes a dedicated signing module. This module allows users to import digital certificates and apply signatures to documents.
The signing process is straightforward: load your PDF‚ select the signing function‚ choose your certificate‚ and position the signature. PDFsam Enhanced provides options for creating signature appearances and managing multiple certificates. The Basic version‚ while lacking direct signing‚ can be used in conjunction with other tools to prepare PDFs for signing. It’s a versatile option for those already familiar with PDFsam’s other features‚ offering a combined workflow.

Command-Line Tools in Detail
Leveraging command-line tools like openssl and qpdf provides powerful‚ scriptable PDF signing capabilities on Linux‚ offering granular control and automation.
Detailed Guide to `openssl` and PDF Signing
Utilizing openssl for PDF signing involves a multi-step process‚ demanding careful attention to detail. First‚ you’ll need a digital certificate and private key; openssl doesn’t directly sign PDFs; instead‚ it’s used to create a detached signature file. This requires converting the PDF into a raw byte array‚ signing that array with your private key‚ and then embedding the signature into the PDF.
The process typically involves commands to hash the PDF content‚ sign the hash with your private key‚ and then utilize a tool like pdftk to embed the signature into the PDF file. Verification relies on the recipient having access to your public certificate to validate the signature’s authenticity. While complex‚ openssl offers a highly customizable and secure method for digitally signing PDFs on a Linux system‚ suitable for automated workflows.
Advanced Usage of `qpdf` for Signature Verification
Beyond basic signing‚ qpdf excels in advanced PDF signature verification. It allows detailed inspection of signature dictionaries‚ revealing information about the signing certificate‚ the signing time‚ and the employed hashing algorithm. You can use qpdf to check the validity of the certificate chain‚ ensuring it hasn’t been revoked and is trusted by your system.
Furthermore‚ qpdf can identify if the PDF has been altered after signing‚ a crucial security check. It achieves this by recomputing the hash of the document content and comparing it to the hash stored within the signature. Advanced users can leverage qpdf’s scripting capabilities to automate signature verification processes‚ integrating them into larger document management systems. This ensures ongoing document integrity and compliance.
Certificate Management on Linux
Secure PDF signing on Linux necessitates careful certificate handling‚ encompassing generation‚ secure storage‚ and efficient management for reliable digital signatures.
Generating a Digital Certificate
Creating a digital certificate on Linux is foundational for secure PDF signing. While commercial Certificate Authorities (CAs) offer trusted certificates‚ generating a self-signed certificate is viable for testing or internal use. This typically involves using openssl‚ a powerful command-line tool. The process begins with generating a private key‚ which must be kept secure.
Next‚ a Certificate Signing Request (CSR) is created‚ containing information about the certificate holder. This CSR is then used to generate the self-signed certificate. Remember‚ self-signed certificates lack the trust of established CAs‚ so recipients may encounter warnings. For production environments‚ obtaining a certificate from a recognized CA is strongly recommended to ensure broader acceptance and trust in digitally signed documents. Proper key management is crucial throughout this process.
Importing and Managing Certificates with KeyStore Explorer
KeyStore Explorer provides a graphical interface for managing digital certificates and private keys on Linux systems. After generating or obtaining a certificate‚ importing it into a keystore is essential for applications like LibreOffice or Okular to access it for signing. KeyStore Explorer supports various keystore types‚ including JKS and PKCS#12.
The process involves opening the keystore file (or creating a new one)‚ then importing the certificate chain and associated private key. Securely storing the keystore password is paramount. KeyStore Explorer allows you to view certificate details‚ export certificates‚ and manage key pairs. It simplifies certificate management‚ especially for users unfamiliar with command-line tools‚ ensuring a streamlined PDF signing workflow.

Troubleshooting Common Issues
PDF signing can encounter validation or recognition errors; these often stem from certificate problems or incorrect configurations within signing applications.
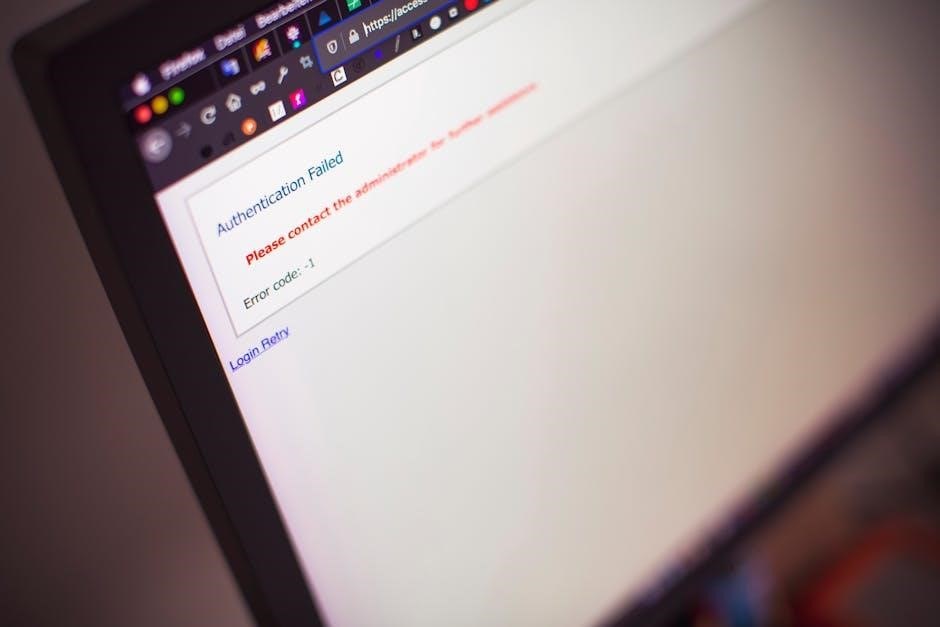
Signature Validation Errors
Encountering signature validation errors when working with digitally signed PDFs on Linux is a common challenge. These errors typically indicate a problem with the signature itself‚ the certificate used to create it‚ or the environment attempting to validate it. Several factors can contribute to this issue. The certificate might be expired‚ revoked‚ or not trusted by the system validating the document.
Incorrect certificate chain configuration is another frequent cause; the validating application needs the complete chain of trust to verify the signature. Furthermore‚ modifications to the PDF after signing invalidate the signature‚ as any change alters the document’s hash. Ensuring the document remains unaltered post-signature is crucial. Finally‚ compatibility issues between different PDF readers or signing tools can sometimes lead to validation failures‚ necessitating testing across various platforms.
Certificate Not Recognized Errors
“Certificate Not Recognized” errors during PDF signing on Linux often stem from issues with trust and certificate store configuration. The system or application attempting to use the certificate doesn’t inherently trust the issuing Certificate Authority (CA). This typically requires importing the root CA certificate into the system’s trusted store.
Another common cause is an improperly installed or configured certificate. The certificate file might be corrupted‚ have incorrect permissions‚ or not be correctly linked to the corresponding private key. Furthermore‚ some applications may have their own separate certificate stores‚ requiring the certificate to be imported into those specific locations. Ensuring the certificate is valid‚ properly installed‚ and the CA is trusted are essential steps for resolving these errors‚ alongside verifying compatibility with the chosen signing tool.

Best Practices for PDF Signing
Prioritize robust key protection and signature validity checks when signing PDFs on Linux‚ mirroring the security demands of growing digital appointment systems.
Ensuring Signature Validity
Maintaining signature validity is paramount when utilizing PDF signing on Linux‚ especially as digital workflows‚ like appointment booking software‚ become more prevalent. Regularly verify signatures using trusted tools – qpdf offers advanced verification capabilities. Ensure the certificate used remains valid and hasn’t been revoked; certificate authorities provide revocation status checks.
Timestamping signatures is crucial; it proves the document existed in its current form at a specific time‚ preventing later claims of alteration. Employ long-term validation (LTV) profiles‚ embedding necessary revocation information within the PDF itself. Consider the evolving digital signature standards and update signing processes accordingly. A valid signature assures recipients of document authenticity and integrity‚ mirroring the trust required in digital appointment confirmations.
Protecting Your Private Key
Your private key is the cornerstone of secure PDF signing on Linux; its compromise renders all digital signatures invalid. Store it securely‚ ideally using a Hardware Security Module (HSM) – a future trend in PDF signing – or a robust key management system; Avoid storing the key on easily accessible locations like shared drives or unencrypted storage.
Implement strong access controls‚ limiting key access to authorized personnel only. Regularly audit key usage and monitor for any suspicious activity. Consider using passphrase protection for your key‚ adding an extra layer of security. As appointment booking apps and digital documents proliferate‚ safeguarding your private key is vital for maintaining trust and preventing fraudulent activity. Backups should be encrypted and stored offline.

Future Trends in PDF Signing on Linux
Integration with Hardware Security Modules (HSMs) and advancements in digital signature standards will enhance security and streamline PDF signing processes on Linux systems.
Integration with Hardware Security Modules (HSMs)
The future of secure PDF signing on Linux is inextricably linked to the adoption of Hardware Security Modules (HSMs). These dedicated hardware devices offer a significantly higher level of security for private key storage compared to software-based solutions. HSMs protect cryptographic keys from compromise‚ even in the event of a system breach‚ ensuring the integrity and non-repudiation of digital signatures.
Integrating Linux-based PDF signing workflows with HSMs involves utilizing PKCS#11 interfaces‚ allowing applications to securely access and utilize the keys stored within the HSM. This approach is particularly crucial for organizations handling sensitive documents or requiring compliance with stringent security regulations. As appointment booking and other digital processes grow‚ robust security becomes paramount‚ making HSM integration a key trend.
Expect to see increased support for HSMs within existing PDF signing tools on Linux‚ alongside the development of new solutions specifically designed to leverage the enhanced security capabilities they provide.
Advancements in Digital Signature Standards
The landscape of digital signature standards is continually evolving‚ impacting PDF signing on Linux. Current standards‚ like PAdES (PDF Advanced Electronic Signatures)‚ are being refined to enhance long-term validation and interoperability. Future advancements will likely focus on increased resistance to quantum computing threats‚ necessitating the adoption of post-quantum cryptography algorithms.
These new algorithms will require updates to existing PDF signing tools and libraries on Linux to ensure continued compatibility and security. The move towards more robust standards is driven by the increasing reliance on digital documents for legally binding agreements and the growing sophistication of cyber threats. As appointment scheduling and related digital transactions increase‚ signature reliability is vital.
Expect to see wider adoption of standards promoting remote signing and improved signature appearance consistency across different PDF viewers and platforms.
